Neighbor’s Wi-Fi Hacking / Airslax – Hacking Guide: Unleashing the Power of Wireless Networks
Introduction
Welcome to the ultimate guide on Neighbor’s Wi-Fi hacking and the Airslax tool. In this comprehensive article, we will delve into the intriguing world of hacking wireless networks, exploring the techniques, tools, and precautions necessary to gain access to a neighbor’s Wi-Fi network. Please note that the information provided here is solely for educational purposes, and any misuse of this knowledge is strictly discouraged. Let’s begin our journey into the realm of neighbor’s Wi-Fi hacking!
Neighbor’s Wi-Fi Hacking / Airslax – Hacking Guide
Understanding the Basics of Wi-Fi Hacking
Before we dive into the intricacies of neighbor’s Wi-Fi hacking, let’s first grasp the fundamentals of Wi-Fi networks and their vulnerabilities. Wi-Fi, short for Wireless Fidelity, enables devices to connect to the internet without the need for physical cables. This convenience, however, comes with inherent security risks that can be exploited by skilled hackers.
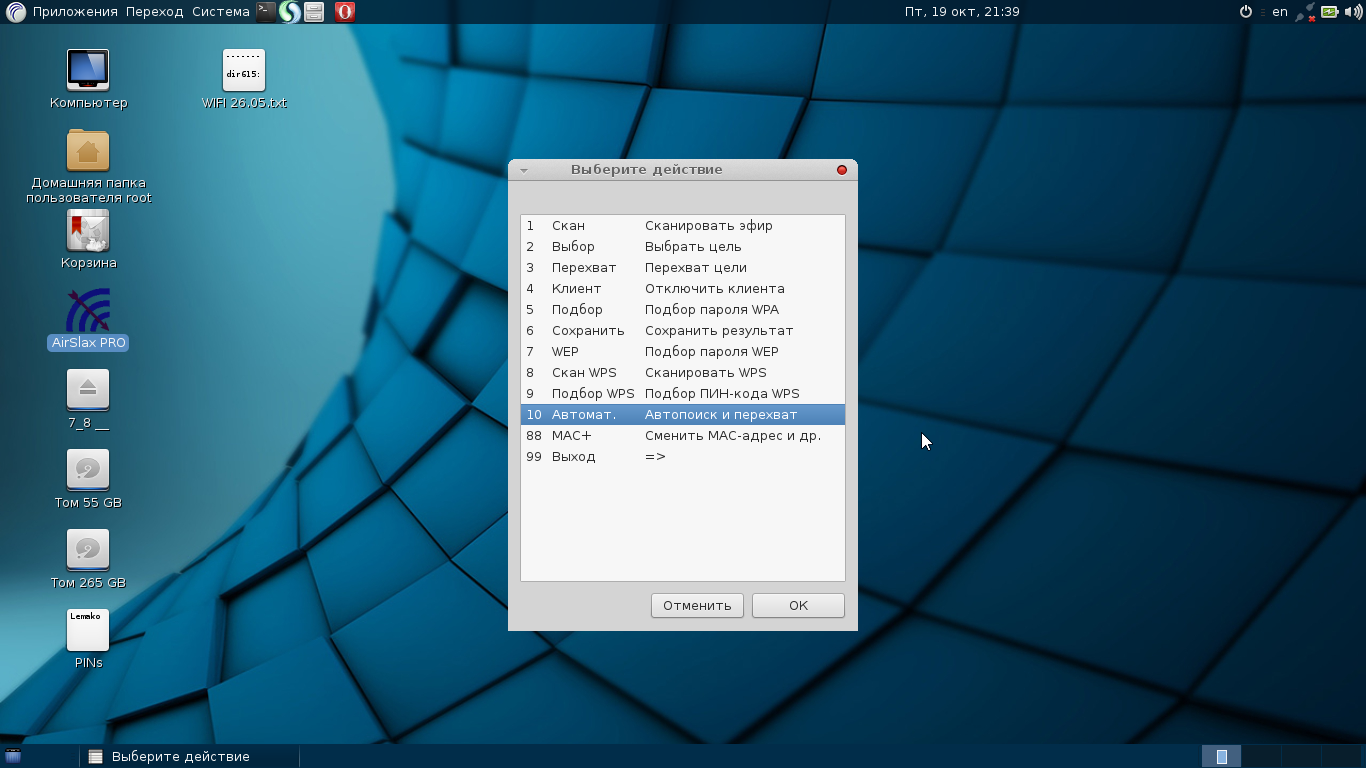
Airslax: The Ultimate Wi-Fi Hacking Tool
Airslax is a powerful and versatile tool widely used for Wi-Fi hacking purposes. It provides an array of features and capabilities that assist hackers in penetrating wireless networks. With Airslax, you can conduct various attacks, including password cracking, network sniffing, and exploiting vulnerabilities in Wi-Fi protocols.
Exploring Wi-Fi Security Protocols
To effectively hack a neighbor’s Wi-Fi network, it is crucial to familiarize yourself with the different security protocols commonly employed. The most widely used protocols include WEP (Wired Equivalent Privacy), WPA (Wi-Fi Protected Access), and WPA2 (Wi-Fi Protected Access II). Each protocol has its strengths and weaknesses, and understanding them is vital for successful hacking attempts.
Step-by-Step Neighbor’s Wi-Fi Hacking Process
Now, let’s walk through a step-by-step guide on how to hack your neighbor’s Wi-Fi network using Airslax. Remember, this guide is for educational purposes only, and it is essential to obtain proper authorization before attempting any hacking activities.
Step 1: Gathering Information
The initial phase involves collecting information about the target network. This includes identifying the Wi-Fi network name (SSID), determining the security protocol in use, and identifying potential vulnerabilities associated with the specific router model.
Step 2: Capturing Handshake Packets
Once you have gathered the necessary information, the next step is to capture handshake packets exchanged between a client device and the router. These packets contain crucial authentication data that can be used to crack the Wi-Fi password.
Step 3: Cracking the Wi-Fi Password
After capturing the handshake packets, the next step is to crack the Wi-Fi password using specialized tools available in Airslax. This process utilizes brute-force techniques or dictionary attacks to decrypt the captured packets and uncover the password.
Step 4: Gaining Access to the Network
Once you have successfully cracked the Wi-Fi password, you can now connect to the neighbor’s Wi-Fi network using the obtained credentials. Exercise caution and use the access responsibly and legally.
Frequently Asked Questions (FAQs)
Q: Is neighbor’s Wi-Fi hacking legal?
A: No, unauthorized access to someone else’s Wi-Fi network is illegal in most jurisdictions. It is crucial to respect privacy and adhere to ethical hacking practices.
Q: Can Airslax hack any Wi-Fi network?
A: While Airslax is a powerful tool, its effectiveness depends on the security protocols and vulnerabilities present in the target Wi-Fi network. Some networks may have advanced security measures that make them harder to crack.
Q: What precautions should I take before attempting Wi-Fi hacking?
A: It is essential to ensure you have proper authorization from the network owner before attempting any hacking activities. Additionally, always use a virtual private network (VPN) to protect your identity and encrypt your internet traffic.
Q: Are there any legal alternatives to hacking a neighbor’s Wi-Fi?
A: Yes, instead of hacking, you can discuss the possibility of sharing Wi-Fi access with your neighbor, setting up your own Wi-Fi network, or using public Wi-Fi hotspots.
Q: What are the potential consequences of unauthorized Wi-Fi hacking?
A: Unauthorized Wi-Fi hacking can lead to severe legal consequences, including fines and imprisonment. It can also damage personal relationships, harm reputations, and result in civil lawsuits.
Q: How can I enhance the security of my Wi-Fi network?
A: To strengthen your Wi-Fi network’s security, use WPA2 or the latest WPA3 encryption, change default login credentials, enable network firewalls, and regularly update your router’s firmware.
Conclusion
Congratulations, you’ve made it to the end of our sarcastic Neighbor’s Wi-Fi Hacking/Airslax Hacking Guide! Remember, hacking someone’s Wi-Fi without permission is illegal and unethical. Instead, focus on enhancing your ethical hacking skills and contributing to the cybersecurity community. Knowledge is power, but it should be used responsibly. Stay curious, stay creative, and always be on the right side of the digital law!
You can also buy instant:


Cashapp Money Transfer Click here
Paypal Money Transfer Click here
Western Union Money Transfer Click here
Venmo Money Transfer Click here
Bank Money Transfer Click here to Contact Us
