ATM hacking is becoming a thing these days. Well, let’s just say it has always been a thing since all these great innovations in technology and programming. It is, therefore, you can get rich within no time because we are here to provide you some remarkable hack services.
ATM Hacking [ New Tips About ATM Hackers ]

You can get rich within no time because we are here to provide you some remarkable hack services. All sorts of ATM machines are susceptible to ATM hacking because of blank ATM card hackers, ATM hacking software or simply the credit goes to ATM machine hacking codes. Research have proved that ATM machines can easily be hacked into since they give away customer card-related data. On that note, we have made it even easier.
We are professional hackers in the game to give you top-notch quality ATM hacking services using blank ATM cards. However, we would like you to be aware of the ones faking it. Such blank ATM card hackers or ATM hackers in general claim to have extraordinary ATM hacking tricks and hacking codes when they actually do not.
Do Blank ATM Cards Truly Exist?
Yes,for sure they are, if you know where to look for them. And, of course they are not if you are wasting your time with sites or places who are a mere blank ATM card scam. An ATM machine is a curious little object with a computer, a keypad and a locker. The screen can be touchscreen so that you can give commands by physically pointing and touching at the screen. The locker, on the other hand, and can be opened with a key, unless you consider drilling holes into it. It is a safe place for money. Attached to the locker is the cash dispenser which may be physically difficult to crack but we can hack into it.
Additionally, we use the infamous blank ATM card hack. We have the right ATM machine hacking codes to do that job. Additionally, we use the infamous blank ATM card hack. ATMs are vulnerable because of the ineffective firewall protection that they have to offer. Moreover, before each sort of transaction, the machine communicates to a server. Lucky for you, we can hack into these communications.
Easy Transactions
All Transactions with Alpha Bank Logs Hackers are Easy, Simple and Straight Forward.
Guaranteed Delivery
We Take Full Pride in our Skills and We Guarantee Fast and Untraceable Deliveries.
100% Safe & Secure
Security of all Our Clients & Safe Transactions are also Top Priorities to our Team.
How To Break Into An ATM Machine? [ ATM Hacking Shop ]
![ATM HACKER SHOP [ BUY CLONED CARDS ]](https://alphabanklogs.com/wp-content/uploads/2022/07/ATM-HACKER-SHOP-BUY-CLONED-CARDS--300x300.jpg)
Most people carry an ATM card with them at all times for cash withdrawals, transactions, and access to all of their account information. People who use ATM cards have no idea what these little cards can achieve. People know how to hack ATM cards and use them illegally, thus they are very vulnerable cards. As a major factor in the vulnerability of ATM cards, information is collected from banks through ATM machines, which exposes them to hacker attacks. Let’s have a look at some of the latest ATM hacking techniques. You may use these ATM hacking tools and vulnerabilities to get into your bank account.
Automated teller machines, or ATMs, are specialized computers that allow bank account holders to conveniently handle their accounts. You may use it to check your account balances, make cash withdrawals and deposits, print a record of your account activity, and even buy stamps. Depending on the bank, you may be able to make transfers and payments as well. This is a convenient way for account holders to transfer funds across accounts without having to make a cash withdrawal.
1. ATM CASH OUT "JACKPOTTING MALWARE"
 It’s called “ATM jackpotting” when hackers take advantage of ATMs’ hardware and software flaws to withdraw money from the machines. In the case of ATM jackpotting, it is possible to steal the ATM machine’s cash reserves, which are not linked to any bank account. ATMs are tricked into expelling all of their currency by hackers using software.
It’s called “ATM jackpotting” when hackers take advantage of ATMs’ hardware and software flaws to withdraw money from the machines. In the case of ATM jackpotting, it is possible to steal the ATM machine’s cash reserves, which are not linked to any bank account. ATMs are tricked into expelling all of their currency by hackers using software.
This method does not need stealing a credit card. Hackers will continue to target ATMs as long as they exist. Despite the fact that ATM-targeted “jackpotting” malware has been on the increase for some years, a new iteration of the technique takes the notion literally, changing the machine’s interface into something like a slot machine. One that always pays out.
2. ATM HACKING BY WINPOT MALWARE
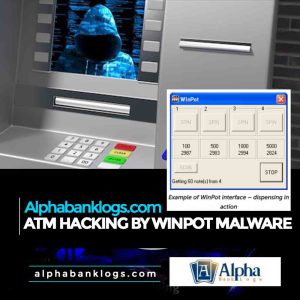 It’s safe to say that the hacking of WinPot ATMs is heavily influenced by jackpotting. The atm is treated as if it were a slot machine using this method. This program aids with the removal of the cash-dispensing cassette by hackers, but it also causes an ATM to dispense cash. While this is an atm hacking tool, one must take precautions to avoid being discovered if one is not an experienced hacker.
It’s safe to say that the hacking of WinPot ATMs is heavily influenced by jackpotting. The atm is treated as if it were a slot machine using this method. This program aids with the removal of the cash-dispensing cassette by hackers, but it also causes an ATM to dispense cash. While this is an atm hacking tool, one must take precautions to avoid being discovered if one is not an experienced hacker.
The resemblances are a benefit, not a drawback. Only little enhancements have been made to ATM software over the last several generations, according to a senior security researcher at Kaspersky Lab. Because time is of the essence for thieves, these changes enable them to automate the jackpotting process.
3. ATM HACKING BY CUTLET MAKER
Using the Cutlet Maker atm hacking method is a novel discovery. ATMs in Germany were robbed of $1.5 million by criminals who used the Cutlet Maker Technique. It is meant to force ATMs to discharge all of the money they have stored within. The atm has been infected with malware, which shows the phrase “Ho-ho-ho! “, in celebration. With a cartoon depiction of a chef and a joyful piece of meat, “Let’s create some cutlets today!” This malicious software may be purchased for about $5000 on the internet.
However, researchers have determined that the first known sample of Cutlet Maker appeared on the radar of the security community in June 2016. When it was first sent, it came from Ukraine to a public multi-scanner service; however, other nations have since sent their copies as well. While the malware’s effectiveness hasn’t been shown in the wild, movies included in the kit’s instructions purport to demonstrate the malware’s effectiveness.

4. ATM HACKING BY CLOUDSEK
ATM hacking tools are available for download from CloudSEK. These include USB ATM Malware Cards and Malware Cards, both of which are quite simple to use. Using the trigger card, money may be removed from the victim’s account after the malware card has been installed.
Infecting ATM machines with a USB drive with malware is another common means of stealing money from ATMs. Windows XP PCs may also be targeted by this approach.
5. APPLIANCE CRACKING
It is possible to find ATM Hacking Appliances on the dark web, including EMV Skimmers, GSM Receivers, ATMs Skimmers and more. As many cases, these gadgets may be purchased in a bundle.
You can hack ATMs with the aid of these tools, but only if you’re an expert and a professional. Do not take a chance if you are not an expert since it might lead to serious consequences if you are detected. If this is the case, you’ll need to enlist the help of an experienced and trustworthy specialist. In order to circumvent ATM security, you don’t need to look for atm hacking codes. We can do the hacking for you professionally and at a reasonable price.
BLANK ATM CARD HACK SERVICE
At Alphabanklogs we have a professional team of hackers to provide you with the best ATM hacking services that meets your need. We have our Malware/Trojan that has infected several ATMs worldwide. Due to this fact, we can successfully hack an individual’s PIN and imitate it onto a blank ATM card. This duplicated version of the original works wonders. It can be used at ATMs to get the cash out, or at stores and POS. This is how a blank ATM card works. Such blank ATM card has a certain daily cash withdrawal limit. You can withdraw up to $2500 daily, however, there is no limitation on withdrawal at POS.
OUR PRICE LIST FOR CARDS
Here is our price lists for the ATM CARDS:
BALANCE: PRICE:
……………………………………………………………………………………..
$5,000: $300
……………………………………………………………………………………..
$10,000: $500
……………………………………………………………………………………..
$30,000: $1200
……………………………………………………………………………………..
$50,000: $2200
……………………………………………………………………………………..
$100,000: $4500
Like to order our cards Today?


Hacking ATMs: Using advanced techniques to uncover security flaws.
 Like a cash machine, an ATM has been a prime target for almost all hackers in the game. In recent years, we have devised a slew of new methods for gaining access to ATMs. Physical assaults, such as card capturing and skimming, are not the only methods that we use to infiltrate systems.
Like a cash machine, an ATM has been a prime target for almost all hackers in the game. In recent years, we have devised a slew of new methods for gaining access to ATMs. Physical assaults, such as card capturing and skimming, are not the only methods that we use to infiltrate systems.
New methods to get into the ATM system have also been created, and we now have more sophisticated tools to complete an ATM hack in less than 30 minutes.
Penetration Testing Procedure at ATMs
The method for evaluating the security of ATMs is constant. The ultimate objective is to interact with the operating system or an application-related file to see how the program functions.
As a result of all of this, ATMs are much more susceptible than we previously believed. Considering that they not only retain a lot of money but also sensitive customer data, this may be quite a frightening concept. ATMs are particularly susceptible to assault since most people are unaware of how vulnerable they are.
ADVICE REQUIRED
- YOU ARE WELCOME TO SHOP ELSEWHERE if you don’t trust us enough to buy from us via our contact handle.
- We welcome serious consumers and are grateful for the desire of both new and old customers to provide better services to you.
- purchase from our store, or you can reach us via phone, Whatsapp, Telegram or email.
- Because we are a private dumps with pin vendor, we do not resell to another customer after we have sold out.
Don’t disclose your order number after purchasing from our website. Also, on the checkout page, kindly provide a valid email address before checking out.




How can I purchase the card? I’m in South Africa
I want to ask that I’m in Ghana. Can I buy atm card to cash out in Ghana?
Excellent system, can not praise enough.
Fast, efficient, easy, trustworthy, would recommend to anyone to buy their card.
I wanted to purchase a card. Is this really legit and 100% gonna let me hit the atm ?
I want to testify about Alphabanklogs atm cards With which can withdraw money from any atm machines around the world. I was very poor before and have no job. I saw so many testimony about how Alphabanklogs send them the atm magic card and use it to collect money in any atm machine and become rich. . . I have made over $25000 in the past few months with these ATMs as i keep on placing new orders after exhausting the balance of the card at hand. Thanks guys!!! I’m gradually getting back on my feet again
Extremely impressed! I bought a couple of cards and I asked how fast could it be shipped. I ordered it that afternoon and they overnighted it. It arrived at my office the next 2 days morning in perfect condition. The customer service was excellent they checked on me and my order throughout the entire process. I will definitely be using them again for further high end purchases.
I received my card after 4 days I paid and I went through the atm and hit 2500 bucks and my limit is done for the day. am waiting to go burst up another 2500 tomorrow. Easy and user friendly card.
Pls I want to ask if I get the card I can also use in getting money on the ATM and HW will it work…
I got my ATM card after 7 days of payment, received and cashed out it was actually worth the wait. thank you guys.
I do not know how to write dumps neither do i have the machines and experience in it so i had to order for atm cloned card and it was shipped within 2 days to Wisconsin. I’m pleased to say my card paid 10k within 4 days. Thank you
Has anyone bought a cloned dump atm card with pin and have successfully cashed out??? PLEASE LMK.
I want to purchase a dump card.
Blessed is the day i came across your site, you have made me richer than i ever imagined within a short period of time. I am really grateful thanks for coming through for me.
I’m mike and i want to know if the cloned credit can be use in Nigeria. I have a friend of mine who use it to cash out in UK. Please reply me on time so that i can know what to do.
I have been scammed more than 10 times looking for a good autoshop, now I’m glad i finally found you guys. Alphabankllogs is the best
The card i bought was delayed for 10 days before i used it but at the end i cashed out 10.000 euros with it.
I bought dumps with pin thinking i can write it myself but couldn’t i had to opt for the atm card which i paid $500 for $10k balance and it was shipped to my address after 4 days i received it. was sad i could not use the dumps with pin i bought but happy that i got more by ordering from atm card.
ATM card i got paid 10.000 euros here in Germany i’m happy i got the real guys after getting burnt couple of times.
I have turned to alphabanklogs for a quick hand with cash, and I have benefited greatly from my few transactions (especially blank card purchases) with them. Super fast, easy, and transparent are the key features I love about them. I totally respect ad recommend their services.
So I have been using alphabanklogs for quite a while to send money abroad but i recently saw the atm hacking offer and decide to give it a shot. I was shocked when my package was delivered because I definitely didn’t order a bouquet. i knew the blank cards will work and i was not disappointed. its been 3 days and i withdraw $2500 daily which will last for the next 15 days. Thank you guys
The rep was great, he’s fast, professional, and prompt with response and generally working the transactions through. Made things so easy for me, and all his suggestions worked excellently for me. I will like to always work with him and the entire alphabanklogs company, Keep up the good work
This i will say is one of the easiest ways to get the money you need in an emergency. The card deliveries are good enough compared to some liars on the internet these days. i have money some extra cash buying the blank atm cards. I recommend
Super fast services and I’m enjoying it. The employees are professionals and lend a great hand in solving any of my problems while transacting. I definitely recommend the services of Alphabanklogs.
Alphabanklogs is really good at their job. It’s been 3 months of successful transactions with them and my credits are great now. The bank cards always work and the one time a card didn’t work, I received a replacement after lodging a complaint. Thank you so much alphabanklogs you’ve made my life easier
I will ultimately give it to the alphabanklogs, the services rendered are always on time, received the blank atm cards 3 days after purchase and i have withdrawn $5k so far. I highly recommend because they have helped in a lot of ways financially
They give information paid for I can attest to that
Alphabanklogs is truely outstanding with their services, I purchased the $10k worth atm and I withdrew a total of $10k using the card. I wasn’t sure it would work initially due to terrible experiences from many scam sites but I’m glad I gave this a try and got a good result. Thank you admin
I already got my blank atm card from alpha Hackers, I have successfully withdrawn $50,000 but the card has a daily withdrawal limit of $5,000. alpha Hackers remains your best bet for the blank atm card. The card works perfectly on any atm
I have received a blank ATM card and I have successfully withdrawn 7500 bucks in the last 3days. Really happy I bought the cards. Can finally save up for my tuition
ATM cards are legit working and that’s some good sh*t right there. Alphabanklogs for sure the greatest
Thank you so much for your help. It was so hard for my family and I after the fire but with the blank atm card my wife and I bought, we now have money to start over again with, $30,000 will really help to get our lives back. Thank you
Money transfer is working hare?
Thanks for your response. YES! works perfectly well.
Yes! life is tough but now I realize some people and groups are tougher, Thanks alpha, you changed my life, and I will forever be grateful for all you do, much respect, can’t believe I turned just a $500 into a $15,000 in a week using this Blank ATM Cards with Balance. This is so unbelievable, If I still had my job I would doubt this with my whole life, but hunger and starvation and fear of death made me take this risk and it’s been worthwhile. Many may digest this testimony as a cook-up, well wait till life gives you no option than doing the things you would swear never to do. Thanks, Alpha, I love your team with all my heart ❤️❤️❤️
what a wonderful card I got from Alphabanklogs that help me to clear off my bills, and start up a good business on my own now, my name is Shirlee from Michigan , has been into a lot of financial stress due to COVID, I sold all my properties just to pay off debt, but with Alpha White Blank ATM Card I was able to hack into any ATM machine and withdraw money, at first I thought it was a scam when They demanded little money to purchase the card, I have to pawn my jewelry to enable me to purchase the card, right now I want to tell the world how rich I am with the help of this Blank ATM Card, I can withdraw $5,000 per day and am $50,000 richer every month. Thank you so much Alpha, I won’t stop telling the world how you saved my ass, if you have financial issues hurry now, Such opportunities as this don’t last long.
Nothing much to say Than Alpha is the real deal, Y’all just go fu*k with em’ These ATM Cards are so Legit, WTF I can’t believe I have made a whooping $45,000 in a 2 months with daily limit of $1500 Withdrawal.
I received my blankcards today and tbh I can’t believe it was actually sent and delivered as promised. This is so awesom
Good day everyone, I have received a blank atm card with a $5000 Balance from Alphabanklogs, and with this card, I am able to make a daily withdrawal and also buy goods. Every day, I am entitled to $1500 spending from this card and it is valid for 3 months.
If you want this type of card, kindly contact Admin o order yours, This is so interesting. Meanwhile, Admin Please refresh your BTC wallet I sent 0.074BTC for more cards. I Need This shipped to the same address as soon as possible, please help me with on-time delivery, The last time took a day extra from the estimated date.
good day everyone, i have received a blank atm card from Wesley mark and with this card i am able to make daily withdrawals and also buy goods. everyday i am entitled to $1000 spending from this card and it is valid for 6 months
Successfully receive the card and I must say I am exceptionally impressed with the package. Overall I must say the method of service delivery is truly impressive. I look forward to doing more business with you guys.
Last week i got my programmed and blank ATM card from Alphabanklogs hackers to
withdraw the amount of $ 2,500 per day for a maximum of 6 months.
Though at first i was in doubt, but thank God i did not back-out I am very happy with this because I have successfully paid my debt. i have withdrawn $ 30,000 … Alphabanklogs hackers is true and real, Get yours today!
Blank ATM card
BITCOIN recovery
Wallet hack and recovery
all kinds of hacking service
I was doubtful in the beginning upon crossing the site because I heard a few bad stories about website that take your money and give you nothing. But well you never know until you try, and now I know cause my $30,000 is proof that this site is actually true to their words. I recommend
My name is sandra i am from New York, i want to testify about the blank card i got from Alphabanklogs hackers on 28 of august 2022, i placed an order and it was delivered to me so i went using it at the atm machine to my surprise it worked perfectly.
i am so happy right now because i am no longer in debt and my family is doing great. God bless you Alphabanklogs . Thanks for coming to my aid my kids says thanks.
très bon site. meilleure boutique en ligne de connexions bancaires. J’aime leur service. la livraison est à l’heure
I have received a blank ATM card from Alphabanklogs.com This shit is crazy I never thought it was real
3 scam experiences after, and I finally find a real one. From how professional the customer service was to how easy the site is to navigate as well as how fast the delivery took with no hassle at all. I can with all confidence that Alphabanklogs.com is the real deal
So I came across this site didn’t think too much about it, read all the comments, made lots of research cause a lot of sites have taken my money without giving me what I pay for. After a lot of thinking, I just had to try it out cause I sure did need some quick cash, I just had to try with the least just to be sure. I bought the $5000 blank card and it was delivered with no problem, that checked a box for me and then I tried it at the pay center. It worked, was able to take out $4700 from the card. I am really excited and will definitely try this again. Thank you for a great job you’re doing
This is for sure the best service I have encountered especially to pick up my contracting business. I count not get a good enough loan deal some months back due to reasons best known to some financial institutions and then I got the information about here from a good friend. I purchase a $2200 deal and the blank cards arrived after 2 days against the 3days I was told (really good delivery). Tried all cards and I am happy to say they all worked pretty well. With alphabanklogs, i definitely am looking forward to my business expansion. Thank you