SQLMap v1.3.7 – Automatic SQL Injection Tool
SQLMap v1.3.7 – Automatic SQL Injection Tool is a powerful and essential tool for security professionals, developers, and ethical hackers. In this comprehensive article, we will delve into the depths of SQLMap v1.3.7, exploring its features, benefits, and practical applications. Let’s embark on a journey to understand this indispensable tool that aids in identifying and addressing SQL injection vulnerabilities.
Introduction
Before we dive into the technical aspects of SQLMap v1.3.7, let’s understand the significance of SQL injection and the role of this remarkable tool in combating such vulnerabilities. SQL injection is a type of cyber attack where malicious actors exploit flaws in an application’s input validation to execute unauthorized SQL queries. These attacks can lead to unauthorized access, data theft, and manipulation.
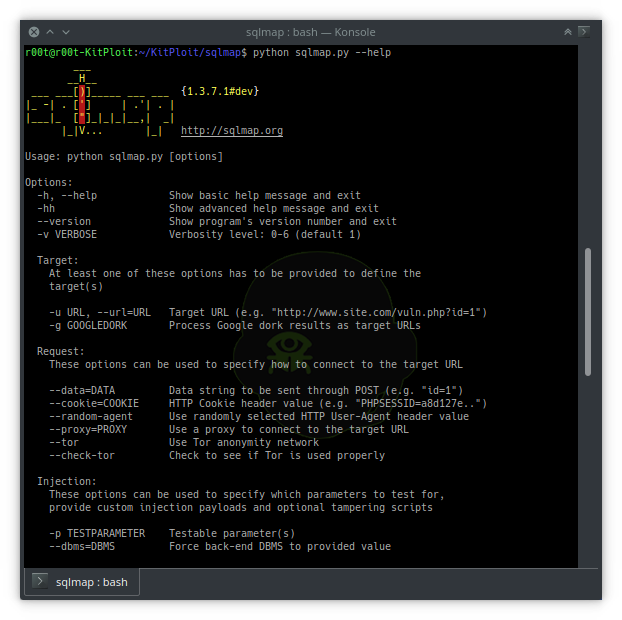
SQLMap v1.3.7 is an open-source penetration testing tool that automates the process of detecting and exploiting SQL injection flaws. Its user-friendly interface, advanced capabilities, and regular updates make it a preferred choice for security enthusiasts and professionals worldwide.
The Basics of SQLMap v1.3.7
In this section, we will explore the fundamental aspects of SQLMap, including its installation and usage.
Installation and Setup
To use SQLMap, you can download it from the official GitHub repository and follow the installation instructions. It is compatible with various operating systems and can be set up easily.
Command Line Interface (CLI) vs. Interactive Mode
SQLMap v1.3.7 provides two modes of operation: Command Line Interface (CLI) and Interactive Mode. The CLI allows for quick and efficient scanning of vulnerabilities, while the Interactive Mode offers a more user-friendly and interactive experience.
Scanning for SQL Injection Vulnerabilities
To scan a target website for SQL injection vulnerabilities, you can use various parameters and options provided by SQLMap v1.3.7. It uses a wide range of SQL injection techniques to identify and exploit potential vulnerabilities.
Extracting Data with SQLMap v1.3.7
One of the key features of SQLMap is its ability to extract data from the target database once a vulnerability is identified. This feature is valuable for understanding the extent of the vulnerability and the potential impact of an attack.
Advanced Techniques with SQLMap v1.3.7
SQLMap v1.3.7 offers advanced techniques that enhance its effectiveness and versatility.
Tampering HTTP Requests
The tool allows users to tamper with HTTP requests, enabling the bypassing of certain security mechanisms and filters. This technique aids in evading detection while scanning for SQL injection vulnerabilities.
Fingerprinting the Database Management System (DBMS)
Understanding the underlying DBMS is crucial for a successful SQL injection attack. SQLMap can automatically identify the type of DBMS used, allowing testers to tailor their attacks accordingly.
Exploiting Blind SQL Injection
Blind SQL injection attacks can be more challenging to detect and exploit. With SQLMap, testers can automate the process of blind SQL injection, making it easier to discover and exploit such vulnerabilities.
Enumerating Users and Databases
Identifying the users and databases within the target system is essential for further penetration testing. SQLMap v1.3.7 provides tools to enumerate this information, aiding in devising effective attack strategies.
Best Practices for Using SQLMap v1.3.7
While SQLMap is a powerful tool, it should be used responsibly and ethically. Following best practices ensures efficient and effective use of this tool.
Permission and Authorization
Before scanning or exploiting a website, ensure you have explicit permission from the website owner or administrator. Unauthorized use of the tool can lead to legal consequences.
Limiting the Impact
Always run SQLMap v1.3.7 with the least privileges required to perform the intended tests. This helps in limiting the potential impact of any accidental or unintentional exploitation.
Keeping the Tool Updated
SQLMap v1.3.7 is actively maintained by a community of developers. Regularly updating the tool ensures you have the latest features, bug fixes, and security patches.
Practical Applications of SQLMap v1.3.7
Now that we have explored the various features of SQLMap v1.3.7, let’s examine some practical applications of this powerful tool.
Website Security Audits
SQLMap is an essential component of website security audits. By scanning websites for SQL injection vulnerabilities, security professionals can identify potential weaknesses and take appropriate measures to fortify the application against potential attacks.
Ethical Hacking and Penetration Testing
Ethical hackers and penetration testers often use SQLMap to assess the security of web applications. The tool allows them to simulate real-world cyber attacks, helping organizations identify and patch vulnerabilities before malicious hackers can exploit them.
Educational Purposes
Cybersecurity students and enthusiasts can use SQLMap v1.3.7 as a hands-on learning tool to understand SQL injection and its implications. By experimenting with the tool in a controlled environment, they can gain valuable insights into web application security.
Incident Response and Forensics
In the aftermath of a security breach, SQLMap v1.3.7 can assist incident response teams in analyzing the attack and understanding how the SQL injection vulnerability was exploited. This information is crucial for preventing future incidents.
Vulnerability Research
Security researchers can use SQLMap to analyze new or undocumented SQL injection techniques. By exploring the tool’s capabilities and behavior, they can contribute to the overall knowledge and understanding of web application security.
Common Mistakes to Avoid with SQLMap v1.3.7
While SQLMap v1.3.7 is a valuable tool, users should be aware of common mistakes that can hinder its effectiveness.
Blindly Trusting Automated Results
Though SQLMap v1.3.7 automates much of the testing process, it’s crucial not to blindly trust the results. Manual verification is necessary to confirm the presence of vulnerabilities and the accuracy of the findings.
Not Using Proper Authorization
Using SQLMap without proper authorization is illegal and unethical. Always obtain explicit permission from the website owner before conducting any security testing.
Neglecting Regular Updates
Failing to keep SQLMap updated can lead to missing out on critical features and security fixes. Regularly updating the tool ensures you have the latest version with improved capabilities.
Real-Life Case Studies
Let’s explore some real-life case studies where SQLMap played a significant role in identifying and mitigating SQL injection vulnerabilities.
Case Study 1: E-commerce Website
A popular e-commerce website suffered a security breach, and customer data was compromised. Upon investigation, it was discovered that the attackers exploited a SQL injection vulnerability to gain unauthorized access to the backend database. By using SQLMap v1.3.7, the website’s security team identified the vulnerability and promptly patched it, preventing further data breaches.
Case Study 2: Financial Institution
A financial institution’s online banking application was targeted by hackers attempting to steal sensitive financial data. Thanks to regular security audits and the use of SQLMap, the institution’s cybersecurity team detected and neutralized the SQL injection attempts before any harm was done.
Frequently Asked Questions (FAQs)
Let’s address some common questions related to SQLMap Injection Tool.
- Can beginners use SQLMap v1.3.7 effectively?Absolutely! While some technical knowledge is beneficial, SQLMap provides a user-friendly interface and extensive documentation, making it accessible to beginners.
- Is SQLMap v1.3.7 legal to use?Yes, SQLMap is legal to use for legitimate penetration testing and security assessment purposes. However, using it without proper authorization on someone else’s website is illegal and unethical.
- Does SQLMap v1.3.7 work on all platforms?Yes, SQLMap is designed to work on various platforms, including Windows, Linux, and macOS.
- How frequently is SQLMap v1.3.7 updated?The SQLMap community actively maintains and updates the tool to address bugs, add new features, and ensure compatibility with the latest security standards.
- Is SQLMap v1.3.7 the only tool for SQL injection testing?There are other SQL injection testing tools available, but SQLMap stands out due to its automation, versatility, and wide range of features.
- Can SQLMap v1.3.7 cause any damage to the target website?When used responsibly and with permission, SQLMap is designed to avoid causing any damage to the target website. However, improper use can lead to unintended consequences.
Conclusion
SQLMap v1.3.7 – Automatic SQL Injection Tool is a remarkable and indispensable tool for anyone involved in cybersecurity, web application development, or ethical hacking. Its ability to automate the detection and exploitation of SQL injection vulnerabilities simplifies the testing process and helps organizations secure their web applications effectively.
By adhering to ethical practices, obtaining proper authorization, and staying updated with the latest version of SQLMap, users can harness the full potential of this tool for securing digital assets and protecting sensitive data from malicious attacks.
You can also buy instant:


Cashapp Money Transfer Click here
Paypal Money Transfer Click here
Western Union Money Transfer Click here
Venmo Money Transfer Click here
Bank Money Transfer Click here to Contact Us